Introduction: Why Cloud VDI Is Now a Security Architecture Decision
By 2026, Virtual Desktop Infrastructure has become a critical control point in enterprise security architectures. As organizations consolidated applications, data access, and privileged workflows into Cloud VDI platforms, those platforms quietly evolved into high-value attack surfaces.
This shift has changed how security teams evaluate VDI. Performance and usability are no longer the primary concern. Instead, CISOs and security architects ask:
- Where is trust established and enforced?
- How much network exposure does VDI introduce?
- How visible and controllable are user sessions?
- Can VDI operate under a Zero Trust model without relying on legacy VPN assumptions?
This article examines Cloud VDI security in 2026, comparing Thinfinity VDI on Oracle Cloud Infrastructure (OCI), Azure Virtual Desktop (AVD), and Amazon WorkSpaces through the lens of Zero Trust Network Access (ZTNA) and architectural risk.
Cloud VDI as Part of the Enterprise Attack Surface
In early VDI implementations, desktops were treated as isolated execution environments. In modern Cloud VDI, that assumption no longer holds.
Today, Cloud VDI platforms:
- Mediate access to internal applications
- Terminate user authentication
- Handle session persistence
- Often, sit between users and sensitive systems
As a result, Cloud VDI has effectively become an access control plane, whether explicitly designed that way or not.
This makes security architecture, not individual security features, the decisive factor.
Zero Trust and ZTNA: From Concept to Requirement
Zero Trust principles are now well understood: never trust, always verify, assume breach, and enforce least privilege continuously. The practical challenge in 2026 is implementation.
ZTNA has emerged as the preferred mechanism for enforcing Zero Trust, replacing traditional VPN models that implicitly trust network location.
For Cloud VDI, the question is not whether Zero Trust is supported in theory, but how deeply it is embedded into the platform’s architecture.
Azure Virtual Desktop: Zero Trust Through Ecosystem Composition
Azure Virtual Desktop supports Zero Trust by leveraging the broader Azure security ecosystem. Identity validation, conditional access, device posture checks, and monitoring are typically handled through Entra ID and associated Azure security services.
From a security perspective, this approach is powerful but distributed. Trust decisions are enforced across multiple layers: identity, network controls, session hosts, and monitoring services. ZTNA is achievable, but often requires careful orchestration of several components.
This architecture works well for organizations already invested in Azure security tooling and identity governance. However, the security posture of the VDI environment becomes tightly coupled to the correct configuration and ongoing maintenance of multiple services.
In practice, this increases the importance of operational discipline and continuous validation.
Amazon WorkSpaces: Secure by Design, Limited by Abstraction
Amazon WorkSpaces provides a secure default configuration with minimal exposed infrastructure. From a threat-reduction standpoint, this reduces certain risks by limiting administrator error and network exposure.
However, because the service abstracts much of the underlying architecture, security teams have limited visibility and control over how trust is enforced at the session and access level. ZTNA concepts are present, but implicitly implemented rather than explicitly defined and managed.
This model can be effective for organizations that prioritize simplicity and baseline security controls. It is less adaptable for environments that require granular access policies, detailed session visibility, or tight integration with enterprise Zero Trust strategies.
Thinfinity VDI on OCI: ZTNA as an Architectural Core
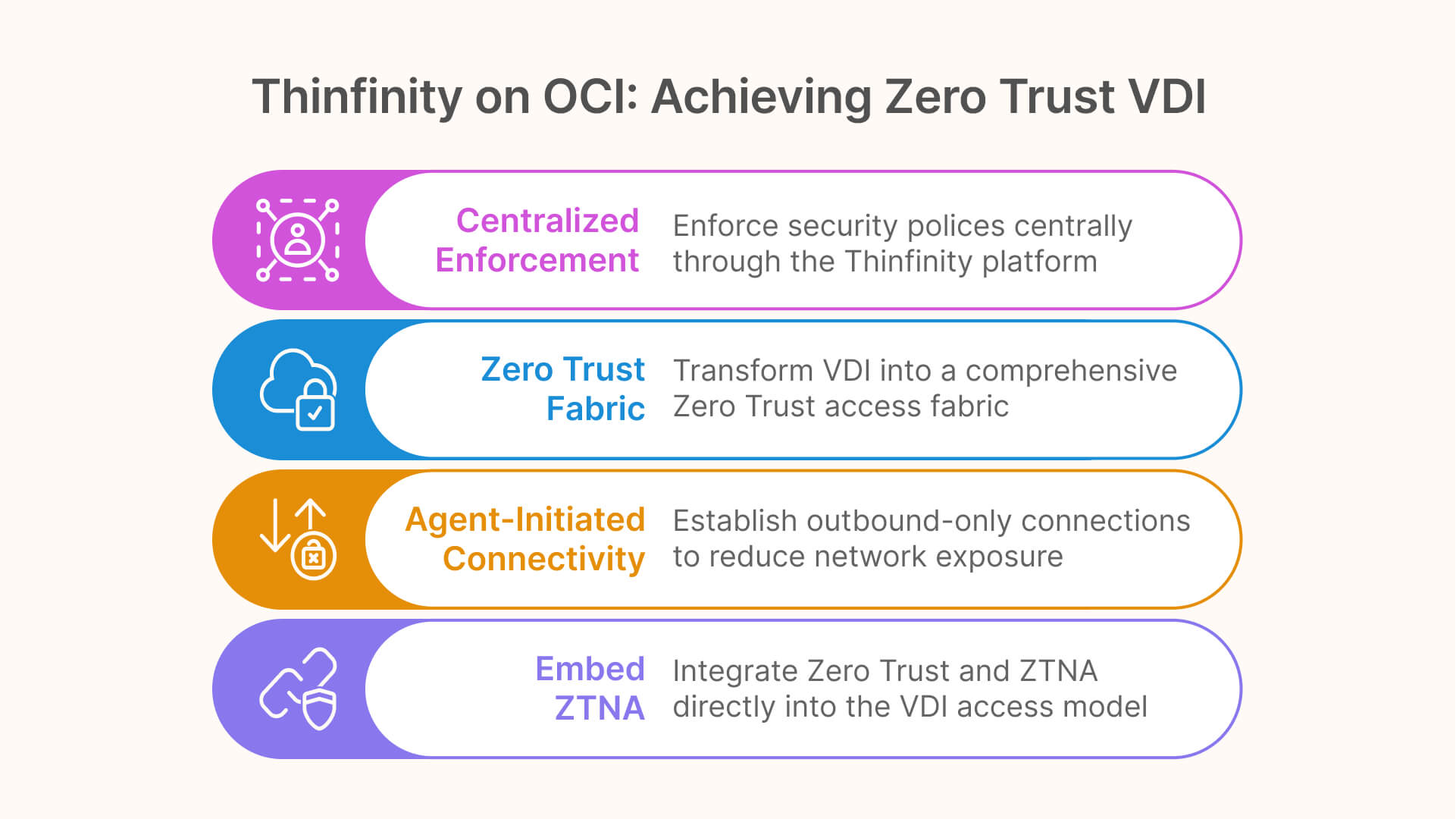
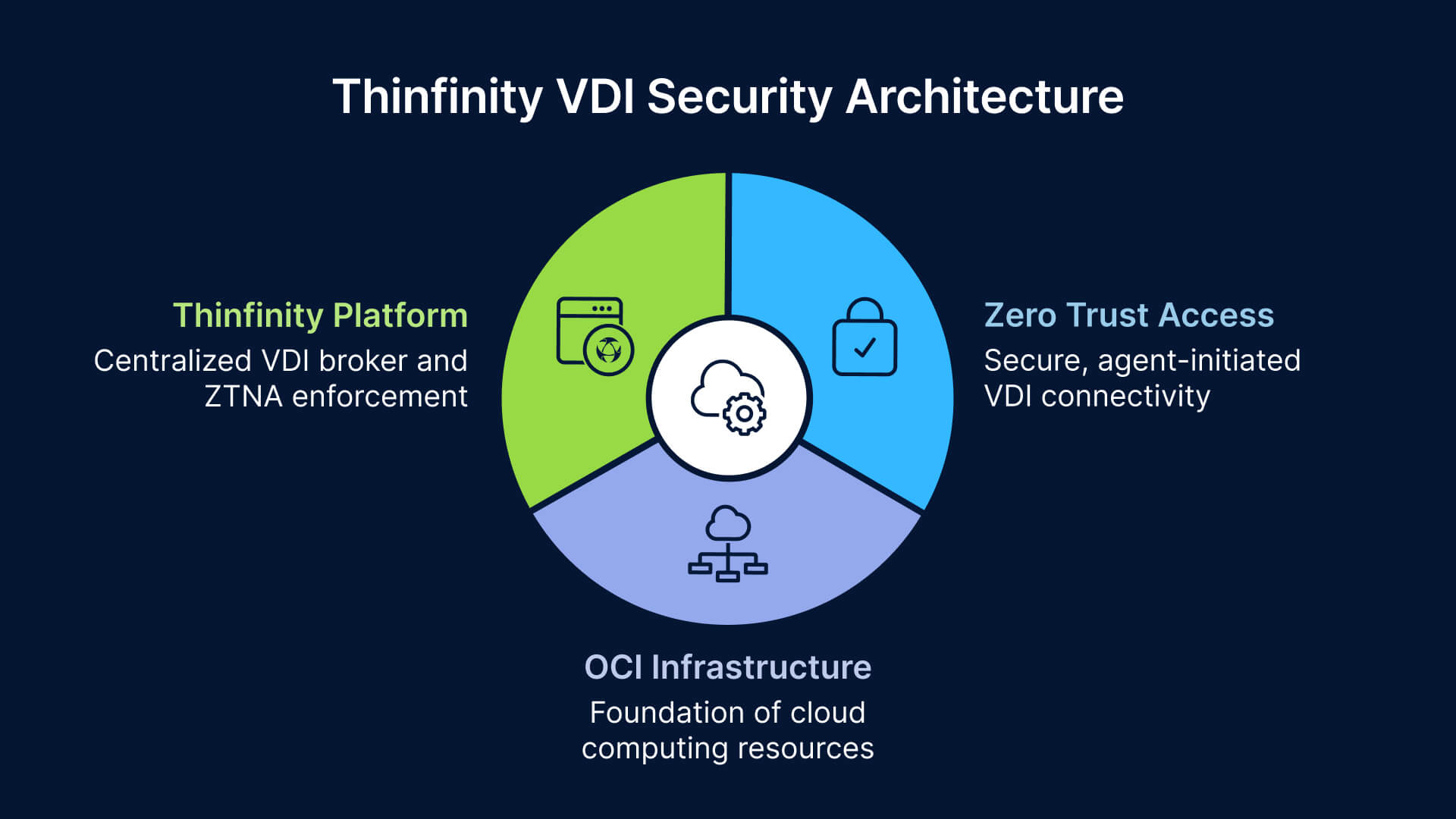
Thinfinity VDI on OCI approaches security from a different angle. Instead of treating Zero Trust and ZTNA as add-ons, it embeds them directly into the VDI access model.
The architecture is based on agent-initiated, outbound-only connectivity. Desktops and applications do not require inbound network exposure, significantly reducing the attack surface. Access is mediated entirely through the Thinfinity platform, which acts as both the VDI broker and the ZTNA enforcement point.
Because Thinfinity operates with only two layers — the platform itself and native OCI infrastructure — trust boundaries are easier to define and reason about. Authentication, authorization, session control, and access policies are enforced centrally, without relying on additional third-party gateways or VPN appliances.
In this model, VDI becomes a Zero Trust access fabric, not just a desktop delivery mechanism.
Session-Level Security and Least Privilege Access
One of the core advantages of ZTNA-aligned VDI is the ability to enforce least privilege at the session level, rather than at the network level.
In traditional VPN-based models, once access is granted, users often gain broad network visibility. In ZTNA-based Cloud VDI architectures, access can be scoped precisely to:
- Specific desktops or applications
- Defined user roles
- Contextual conditions such as identity or policy state
Thinfinity’s centralized control plane enables this granularity by design. Azure Virtual Desktop can achieve similar outcomes, but typically through a combination of identity policies, network segmentation, and monitoring tools. Amazon WorkSpaces offers fewer options for session-level policy differentiation.
From a cybersecurity perspective, reducing lateral movement opportunities is often more important than perimeter hardening.
Visibility, Auditing, and Incident Response
In 2026, security teams expect Cloud VDI platforms to support:
- Detailed session logging
- User activity traceability
- Integration with SIEM and SOC workflows
Architectural clarity plays a significant role here. Platforms with fewer layers and clearer control boundaries tend to produce more coherent audit trails.
Distributed architectures can provide rich telemetry, but correlating events across identity, network, and session layers requires mature tooling and processes. Managed services simplify logging but may limit the depth of available insight.
ZTNA-aligned VDI platforms that centralize access decisions make it easier to answer fundamental incident-response questions: who accessed what, when, and under which policy.
Cloud VDI Security Over Time
Security challenges rarely appear on day one. They emerge as environments scale, users change roles, and access requirements evolve.
In Azure Virtual Desktop environments, maintaining a strong Zero Trust posture depends heavily on governance and continuous configuration management. In Amazon WorkSpaces, security posture is stable but less adaptable.
Thinfinity on OCI emphasizes security through architectural constraint: fewer exposed components, fewer trust boundaries, and centralized policy enforcement. This does not eliminate the need for governance, but it reduces the number of places where security assumptions can fail.
Conclusion: ZTNA Defines the Future of Secure Cloud VDI
In 2026, Cloud VDI security is no longer about perimeter defense. It is about controlling trust at the point of access.
Azure Virtual Desktop, Amazon WorkSpaces, and Thinfinity VDI on OCI all offer secure ways to deliver desktops. The difference lies in how explicitly Zero Trust and ZTNA are embedded into their architectures.
As enterprises move away from VPN-centric models, Cloud VDI platforms that natively support ZTNA principles—minimal exposure, explicit trust, and session-level control—are increasingly viewed not just as desktop solutions, but as core components of modern cybersecurity architecture.


