Manufacturing Workspaces Are Now Infrastructure-Critical
By 2026, the manufacturing workspace is no longer a secondary IT concern. It has become infrastructure-critical, directly influencing production continuity, safety, intellectual property protection, and supply-chain reliability.
Engineers, operators, maintenance teams, planners, external vendors, and partners all depend on continuous digital access to MES, SCADA, quality systems, engineering tools, and analytics platforms. When access fails—or must be shut down due to risk—the impact is immediate and operational.
As a result, manufacturing CIOs and CTOs are reassessing long-standing assumptions about where desktops run, how access is governed, and how quickly environments can be recovered after disruption. This reassessment aligns with Cloud Security and Compliance Best Practices 2026, which emphasize identity-centric access, containment, resilience, and auditability over perimeter-based controls.
Why Traditional Plant-Centric Workspace Models Are Under Pressure
Operational Impact Has Replaced Data Loss as the Primary Risk
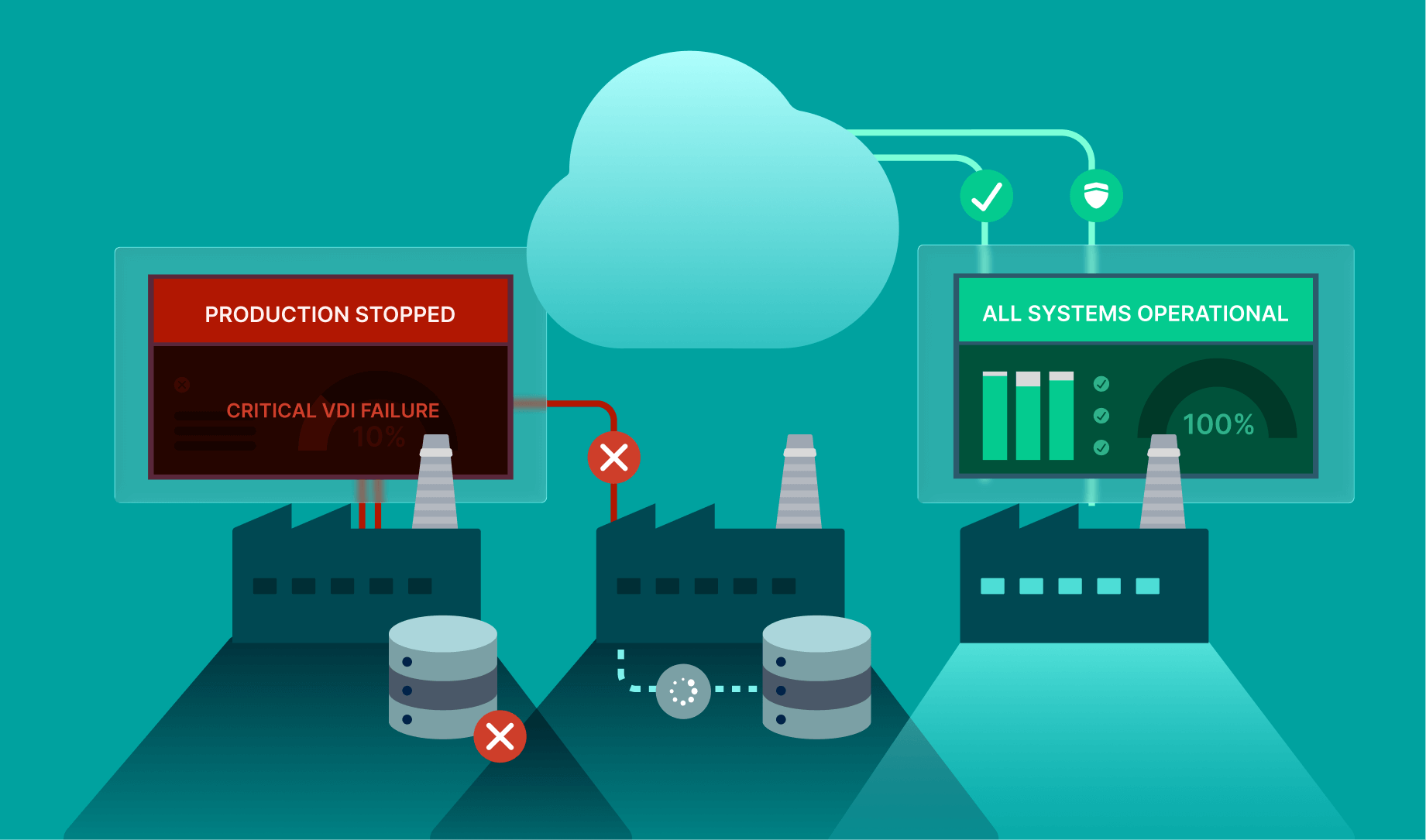
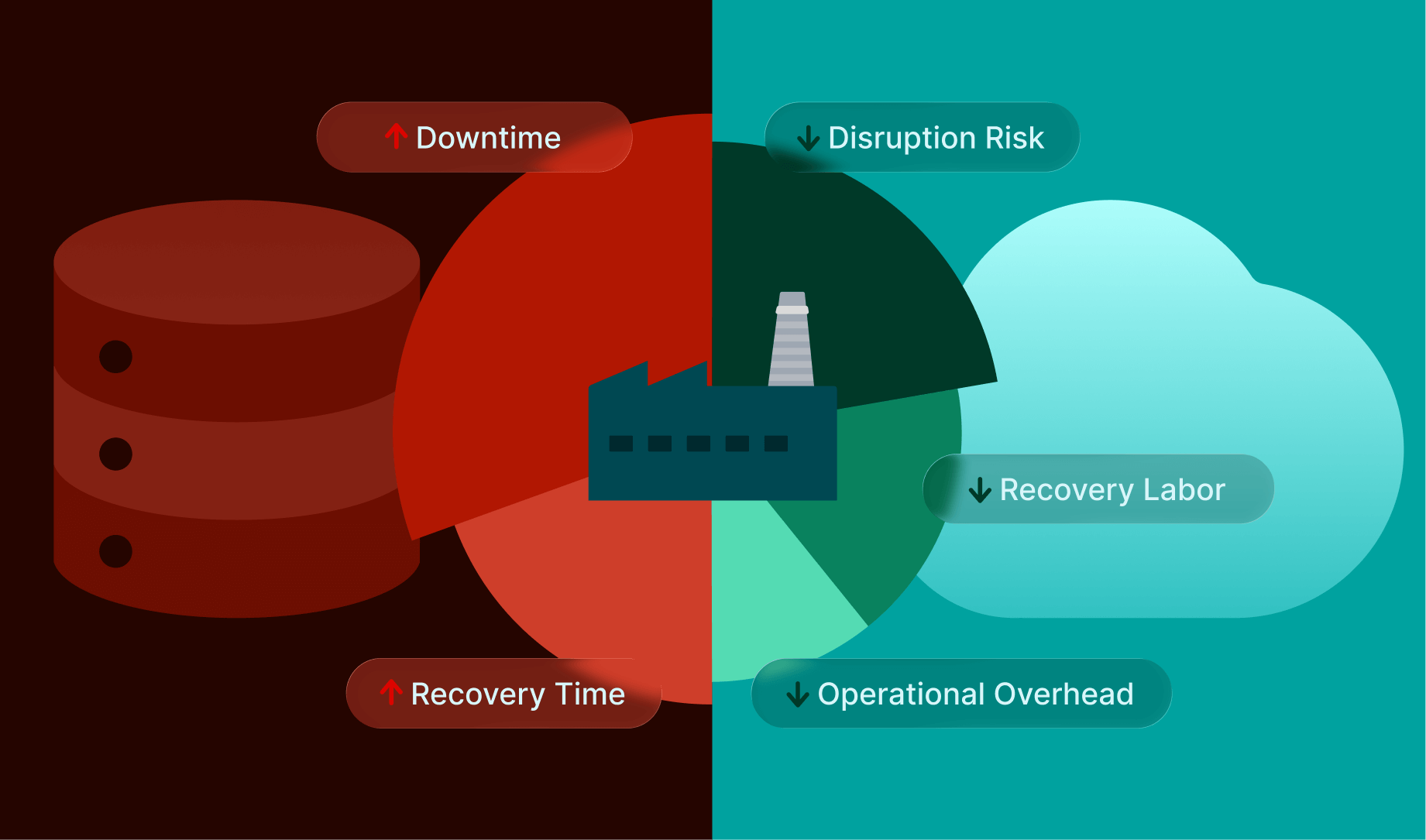
In manufacturing, the most serious incidents are those that interrupt operations. Production stoppages, delayed shipments, safety concerns, and contractual penalties often outweigh the cost of data exposure itself.
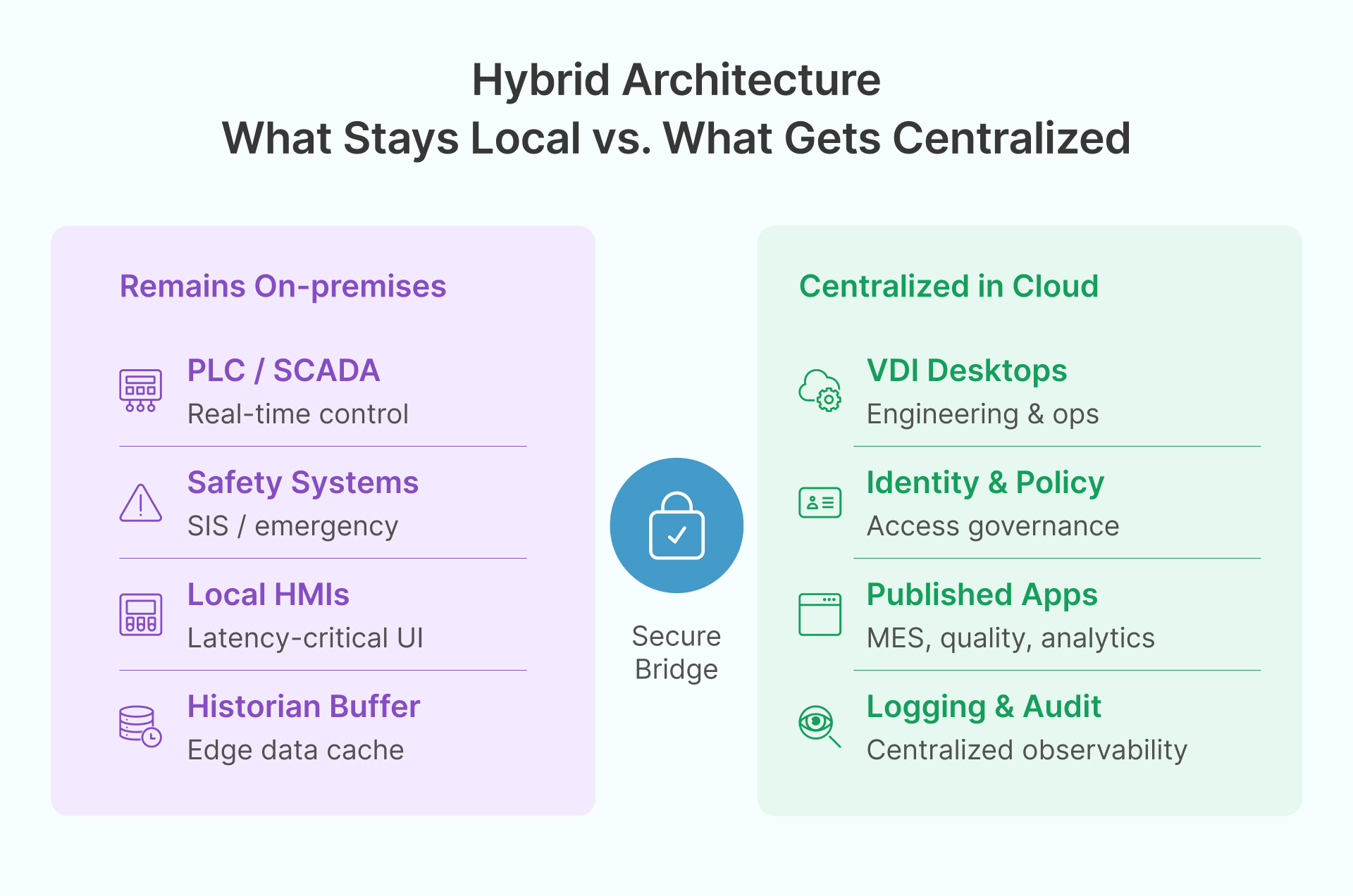
Plant-centric desktop and VDI models distribute applications, credentials, and data across many endpoints. While familiar, this structure makes it difficult to enforce consistent security controls or recover quickly across multiple sites. Each plant effectively becomes its own operational and risk domain.
Centralized workspace models are being reconsidered not primarily for cost reduction, but for their ability to limit blast radius and accelerate recovery when incidents occur.
IT/OT Convergence Has Outgrown Legacy Access Patterns
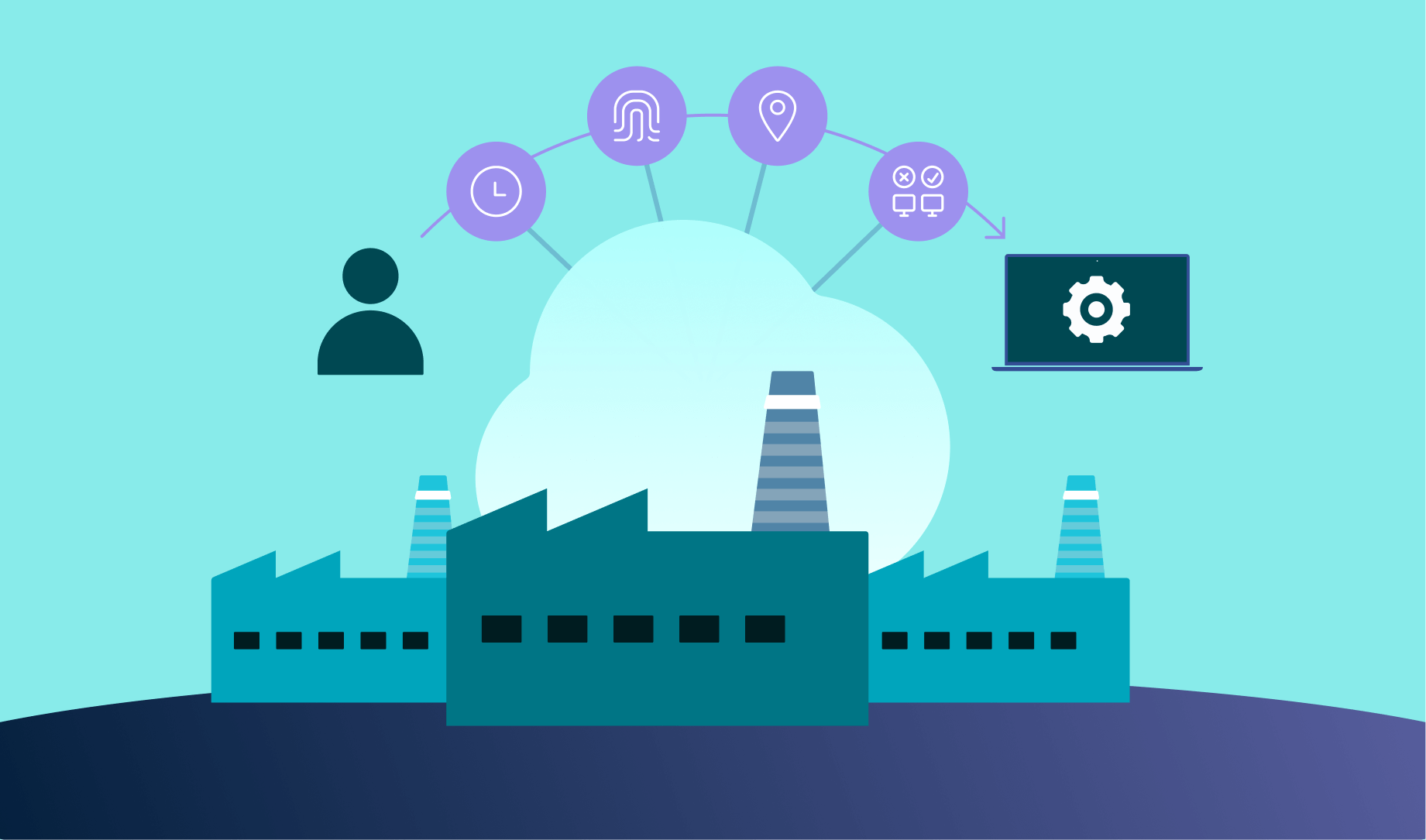
Industry 4.0 initiatives have expanded access needs far beyond traditional office roles. Manufacturing organizations now commonly support:
- Engineers accessing production-adjacent systems remotely
- OEMs and integrators supporting equipment across plants
- Supervisors and planners working with shared operational dashboards
- Cross-functional teams collaborating on digital twins and models
Over time, exceptions accumulate—temporary VPN access, local installs, shared credentials—gradually eroding governance. This creates risk not through intent, but through operational drift.
Here, cloud governance and cloud compliance frameworks intersect with daily operations. The challenge is no longer enabling access, but sustaining consistent control as environments scale and evolve.
Cost, Skills, and Sustainability Are Forcing Architectural Rethinks
By 2026, many manufacturers face a convergence of pressures:
- Aging on-prem infrastructure deployed across plants
- Difficulty maintaining specialized IT skills locally
- Rising energy efficiency and sustainability requirements
- Increased scrutiny on non-differentiating infrastructure spend
While on-prem systems remain necessary in certain latency-sensitive scenarios, CIOs are increasingly questioning whether fully localized workspace stacks remain the most resilient or operationally sound long-term model.
The Role of Cloud Infrastructure in Modern Manufacturing Workspaces
Why Cloud-Based VDI Has Re-Entered Strategic Planning
VDI is not new to manufacturing, but its role has evolved. In 2026, it is less about desktop replacement and more about establishing a control and recovery layer for access to critical systems.
Cloud-based VDI supports:
- Centralized application and desktop delivery
- Identity-driven access enforcement
- Consistent logging and auditability
- Faster recovery using standardized images and pools
These characteristics align with modern cloud risk management approaches, where resilience and observability are as important as prevention.
Why OCI Is Commonly Evaluated for Manufacturing VDI
Oracle Cloud Infrastructure is often included in manufacturing VDI evaluations due to its architectural characteristics rather than industry-specific positioning:
- Clear region and availability domain constructs, supporting multi-plant and multi-region designs
- Performance-oriented networking, relevant for engineering and operational workloads
- Documented reference architectures for VDI and high-performance environments
For CIOs and architects, this reduces design uncertainty and supports repeatability—particularly important for global manufacturing organizations.
Security and Compliance Implications of Cloud VDI
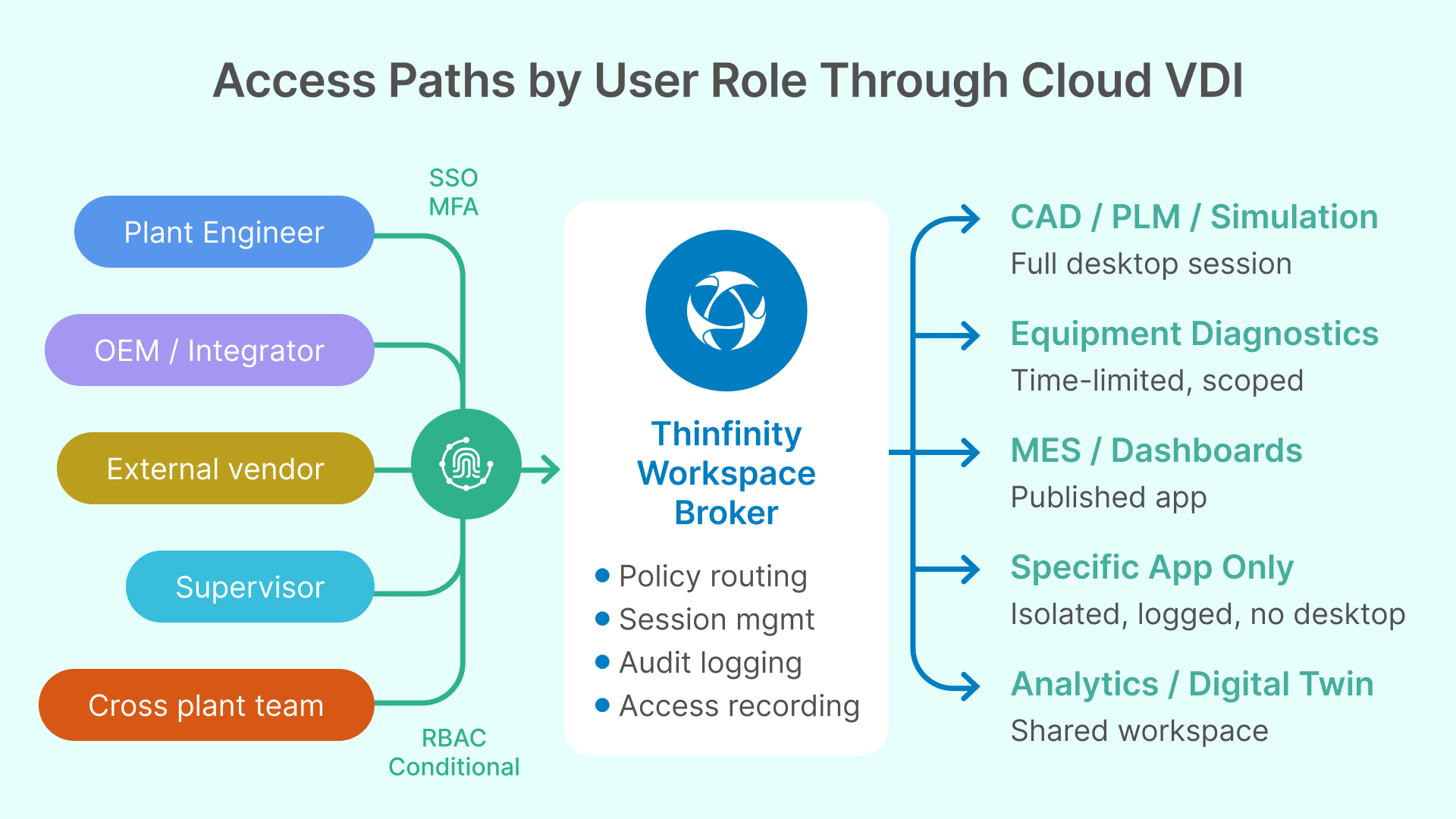
From a governance perspective, cloud-based VDI can support recurring manufacturing requirements such as:
- Centralized identity integration
- Network segmentation and controlled access paths
- Data locality and residency enforcement
- Standardized logging for audits and investigations
These capabilities help align workspace delivery with internal security programs and external frameworks like ISO 27001 and NIST, without tying compliance to individual endpoints.
See How Modern Manufacturing Workspaces Work
Explore how a cloud-based VDI architecture can securely deliver engineering and operational workspaces across plants without disrupting production.
Business Outcomes CIOs Evaluate When Re-Architecting VDI
Security Becomes Enforceable and Observable
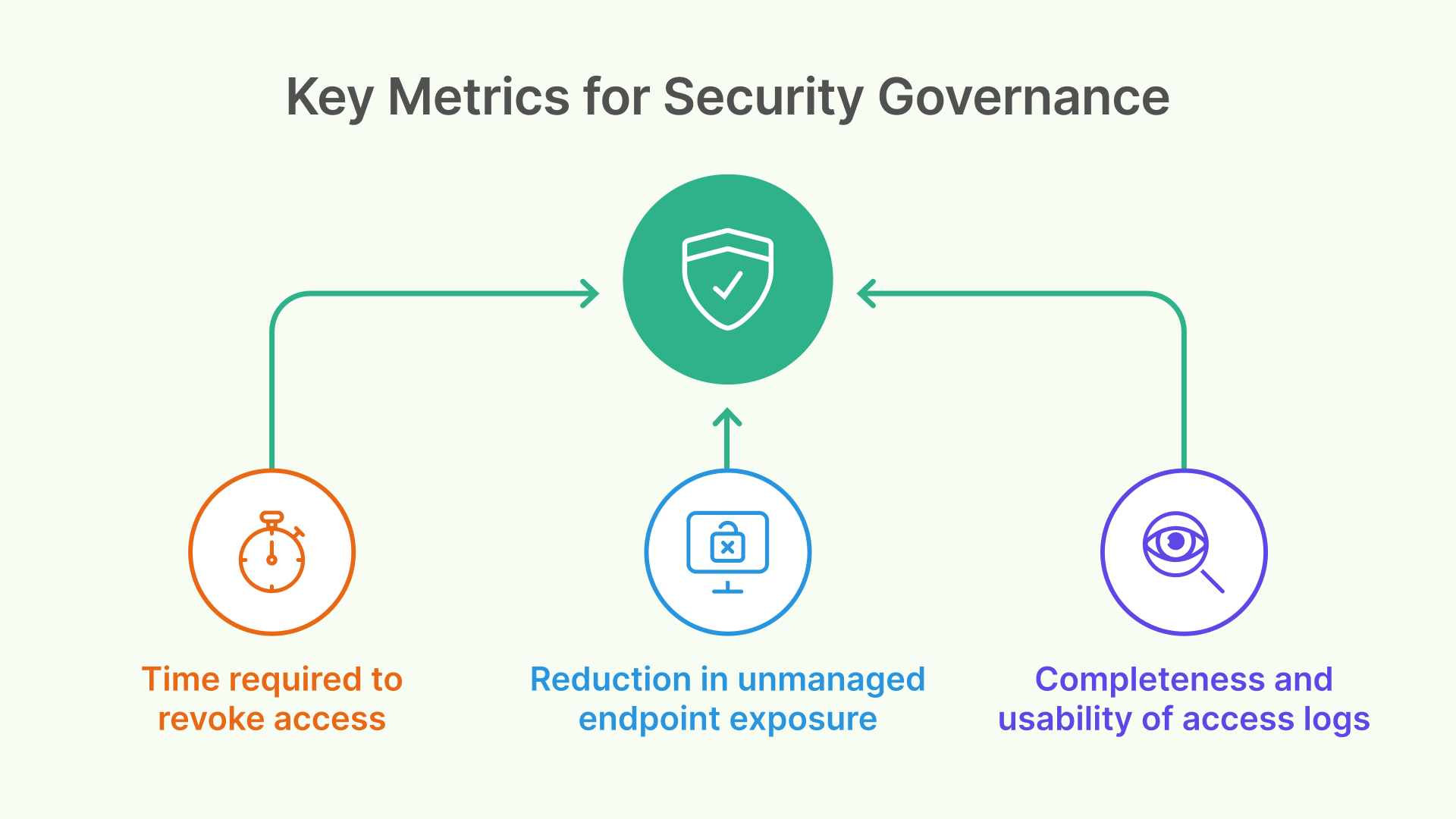
Centralized workspaces make least-privilege access easier to enforce and easier to observe. Visibility into who accessed what, when, and from where improves both incident response and audit readiness.
Resilience Improves at the Operational Level
In a cloud VDI model, recovery shifts from device-level remediation to environment-level restoration. Standardized images and pooled resources allow organizations to restore user access more quickly after disruptions.
For manufacturing, this directly affects downtime and operational continuity—not just IT efficiency.
Standardization Supports Long-Term Modernization
Even when plants retain diverse endpoints—thin clients, rugged devices, legacy HMIs—the workspace layer can be standardized. This consistency simplifies future initiatives such as analytics, AI-assisted operations, and cross-plant collaboration without forcing disruptive endpoint changes.
Where Thinfinity VDI Fits in Manufacturing Architectures
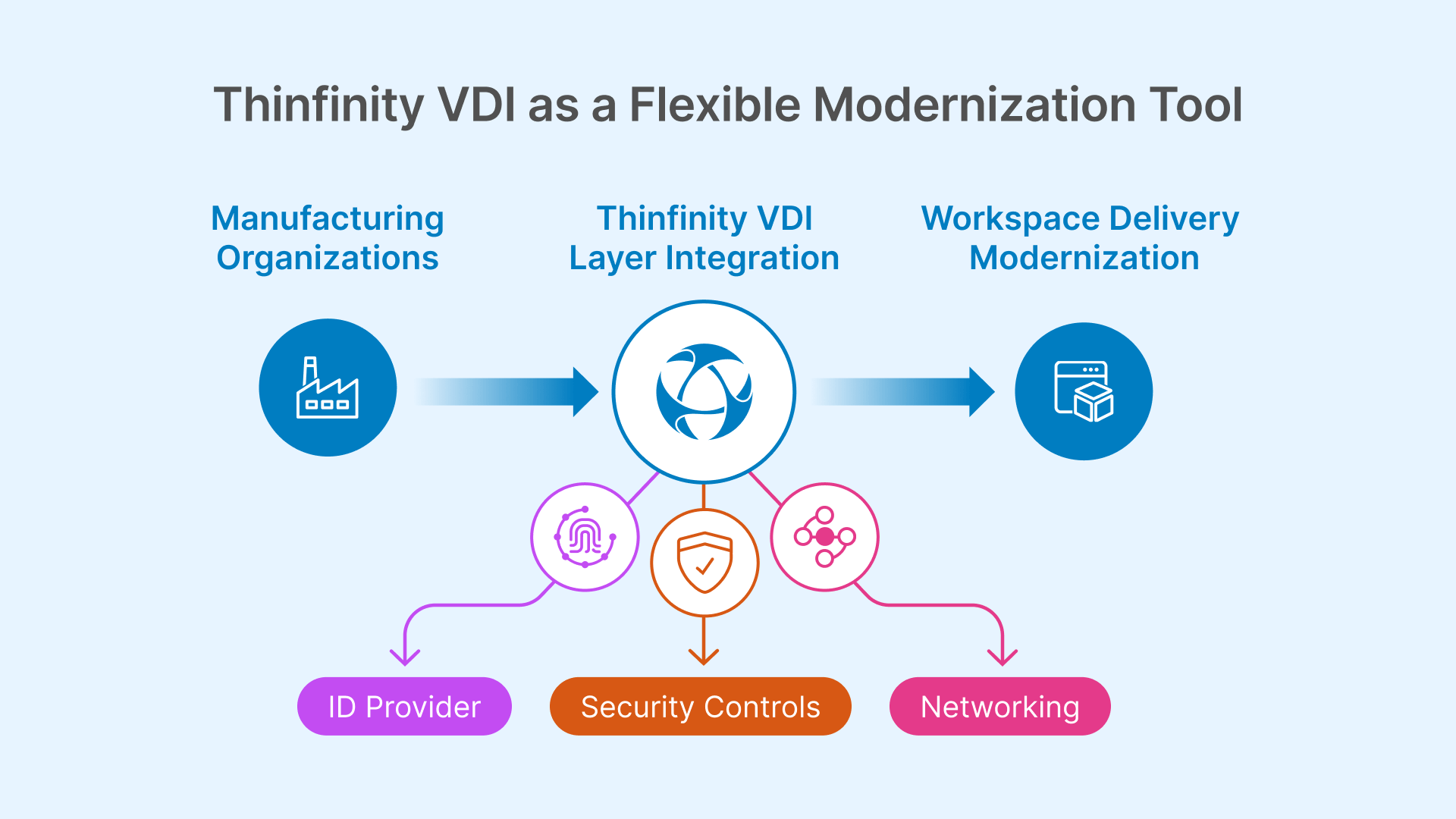
Thinfinity VDI is typically evaluated by manufacturing organizations that need to modernize workspace delivery while preserving architectural flexibility.
In practice, it is used to:
- Centralize delivery of desktops and applications across heterogeneous environments
- Provide controlled access to both legacy and modern workloads
- Support hybrid architectures during phased cloud transitions
Within OCI-based designs, Thinfinity can function as a workspace orchestration layer, integrating with existing identity, networking, and security controls rather than replacing them. This allows organizations to improve access consistency and governance while moving at a pace aligned with operational realities.
Re-Architecting the Workspace as a Manufacturing Control Layer
By 2026, re-architecting VDI is no longer a question of where desktops run—it is a question of how manufacturing organizations control access, manage risk, and recover from disruption.
Manufacturing CIOs are using workspace architecture to create consistency across plants, improve resilience, and enforce governance as environments become more connected and more interdependent. Cloud infrastructure platforms such as OCI provide one viable foundation for this shift, while modern VDI platforms enable it to be implemented incrementally and pragmatically.
The outcome is not “VDI in the cloud,” but a workspace model aligned with how manufacturing actually operates today: distributed, security-conscious, tightly governed, and intolerant of downtime.
FAQ: Manufacturing VDI and Cloud Workspaces in 2026
Why are manufacturers re-architecting VDI now?
Because access, resilience, and recovery have become operational concerns, not just IT optimization topics.
Is cloud-based VDI suitable for shop-floor and OT-adjacent use cases?
Yes, when properly designed. It enables controlled access to operational systems without directly exposing them to external networks.
Does this eliminate the need for on-prem infrastructure?
No. Most manufacturers adopt hybrid models, keeping latency-sensitive components local while centralizing workspace control.
How does this support compliance and audits?
Centralized workspaces improve access traceability, policy enforcement, and logging, which are core audit requirements.
Where does Thinfinity Workspace typically fit in these designs?
It is commonly used as a flexible workspace delivery and orchestration layer that supports gradual modernization across mixed environments.
Further Reading: Dive Deeper Into the Architecture
Explore these resources to understand how the technologies and strategies discussed in this article work in practice—from deployment architecture to Zero Trust access for IT/OT environments.
Thinfinity Workspace Cloud Manager — Full Documentation
Comprehensive technical reference for the Cloud Manager platform: deployment models, broker configuration, cloud orchestration, and infrastructure management for multi-site VDI environments.
Read the docs → DocumentationAccess Management in Thinfinity Workspace v8.5
How to configure identity-driven access, role-based policies, conditional permissions, and session controls—the governance backbone discussed throughout this article.
Read the docs → BlogOT Secure Remote Access: Zero Trust Security for Industrial Environments
A deep dive into how Thinfinity replaces VPNs and jump servers with a Zero Trust approach to SCADA, PLC, and ICS remote access—directly relevant to the OT-adjacent use cases covered here.
Read the article → BlogSecure IT/OT Network Integration with Thinfinity: A Technical Deep Dive
Detailed architecture walkthrough of how Thinfinity Gateway, Primary Broker, and OT Secure Broker enforce network segmentation while enabling cross-domain access—the technical foundation for IT/OT convergence.
Read the article → BlogEnd-to-End Security and Zero Trust: Modern Strategies for Secure Remote Access
Explains the full Zero Trust model underlying this article's architecture: reverse connectivity, TLS-encrypted tunnels, no open inbound ports, and how ZTNA replaces perimeter-based defenses.
Read the article → BlogSecure Remote Desktop: 5 Strategic Priorities for Zero Trust and Hybrid VDI Success
Strategic framework for CIOs modernizing remote desktop access—covers hybrid VDI, VPN elimination, SAML/OAuth integration, and compliance-aligned access controls.
Read the article →