Introduction: Why Security Models in Education Must Change
Universities operate some of the most open digital environments of any large organization. Thousands of students connect daily from unmanaged devices, faculty work from multiple locations, and external collaborators require temporary access to internal systems. At the same time, academic institutions are increasingly targeted by ransomware, credential theft, and lateral movement attacks.
In this context, traditional perimeter-based security models are no longer sufficient. VPN-centric access architectures assume trusted networks and stable user populations—assumptions that do not hold in modern education.
As Virtual Desktop Infrastructure (VDI) becomes a central delivery model for academic computing, Zero Trust principles are emerging as the most viable security framework for universities. This article examines how Zero Trust applies specifically to VDI in education and why VPN-based access is increasingly incompatible with reliable academic environments.
Why VPN-Based VDI Access Breaks at Academic Scale
The Structural Limits of VPNs in Education
VPNs were designed to extend corporate networks to a limited number of trusted users. In universities, they are often stretched far beyond their intended purpose.
Common challenges include:
- Massive concurrent logins at class start times
- Difficulty segmenting access between students, faculty, and staff
- Overexposed internal networks once connected
- Complex client management across personal devices
As VDI usage grows, VPNs become not just a bottleneck but a security liability. When access is granted at the network level, compromise of a single credential can expose far more than intended.
Reliability and Security Are Intertwined
From an executive perspective, security failures are also reliability failures. VPN outages, tunnel instability, or authentication delays during peak hours directly disrupt teaching and learning. Over time, this erosion of trust leads users to seek workarounds, undermining both governance and security posture.
Zero Trust as a Better Model for Academic VDI
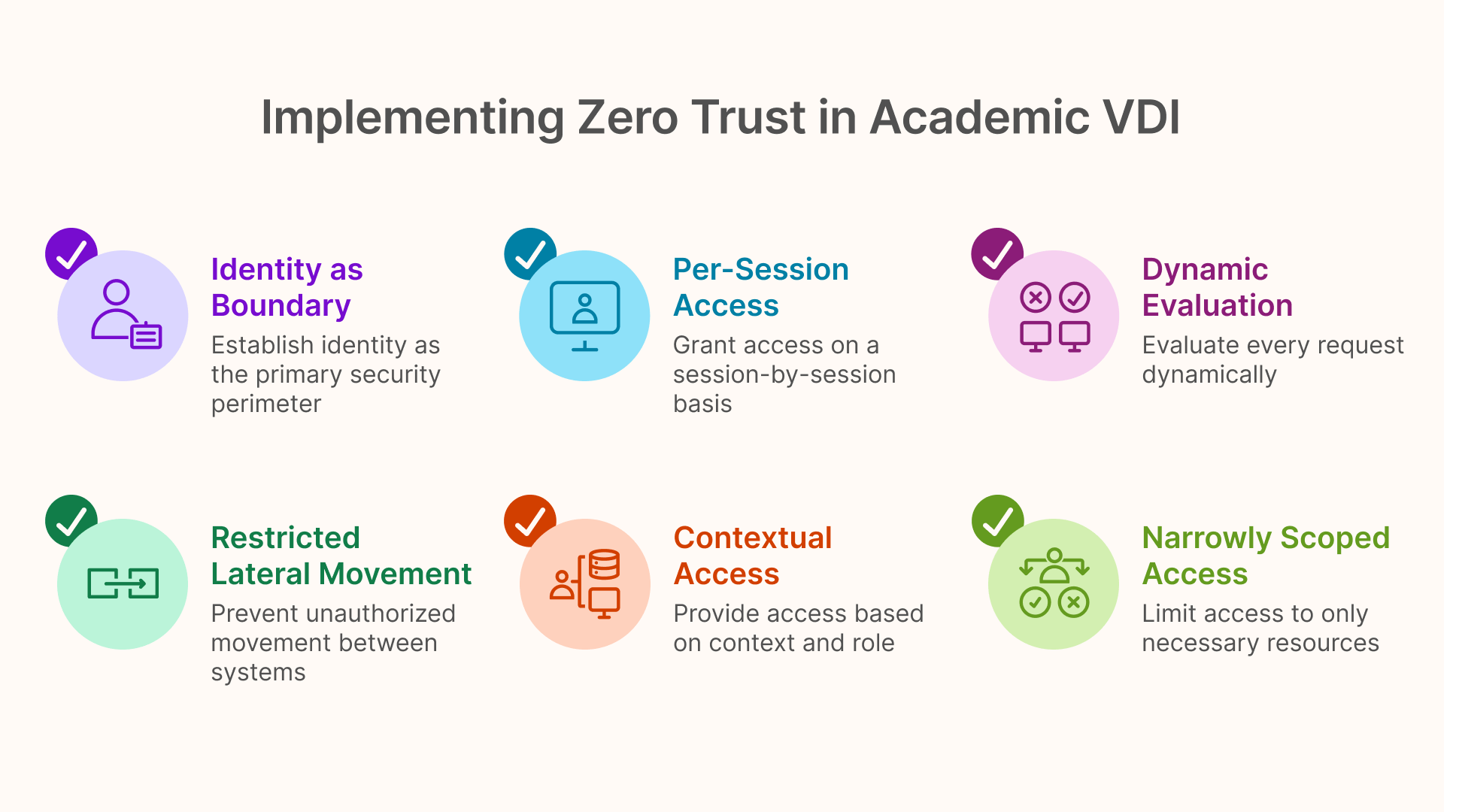
Core Principles Applied to Education
Zero Trust is often summarized as “never trust, always verify,” but in practice it is a design philosophy built around a few core principles:
- Identity is the primary security boundary
- Access is granted per session, not per network
- Every request is evaluated dynamically
- Lateral movement is restricted by default
In academic VDI, these principles translate into access that is contextual, role-aware, and narrowly scoped.
Why VDI Aligns Naturally with Zero Trust
VDI already centralizes execution of applications and desktops. Zero Trust builds on this by ensuring that users:
- Authenticate before session creation
- Only access authorized desktops or applications
- Never gain implicit access to adjacent systems
This alignment allows universities to strengthen security without increasing user friction.
Identity-First Access for Students, Faculty, and Staff
Identity Diversity as a Security Challenge
Educational institutions manage a wide range of identities:
- Short-lived student accounts
- Long-tenured faculty identities
- Administrative and IT staff
- External researchers and partners
Treating all these users equally at the network layer is both inefficient and dangerous.
Role-Based Access in Zero Trust VDI
In a Zero Trust VDI architecture, identity providers become the foundation for access decisions. Users are authenticated through trusted IdPs, and policies determine:
- Which resources are available
- Whether access is persistent or session-based
- What level of monitoring or restriction applies
This approach allows universities to align security controls with academic roles rather than network topology.
Reducing Lateral Movement in Shared Academic Environments
Why Lateral Movement Is a Critical Risk in Education
Universities often host shared resources: file servers, research systems, and departmental applications accessed by many users. Once an attacker gains a foothold, lateral movement can spread rapidly.
Traditional VPN-based access unintentionally facilitates this by placing users “inside” the network.
Session Isolation as a Security Primitive
Zero Trust VDI architectures emphasize:
- Session-level isolation
- Application-level entitlements
- No direct network exposure of internal systems
Even if credentials are compromised, the attacker’s reach is limited to the specific session and resources authorized for that identity.
Zero Trust Without User Friction
Security That Does Not Disrupt Learning
One of the most common objections to stronger security controls in education is fear of user disruption. Students and faculty will not tolerate complex login flows or restrictive device requirements.
Well-designed Zero Trust VDI avoids this by:
- Leveraging existing identity systems
- Eliminating VPN clients
- Providing browser-based access
- Enforcing policies invisibly in the background
When security is embedded in architecture rather than layered on top, it becomes largely transparent to end users.
Thinfinity’s Role in Zero Trust Academic VDI Architectures
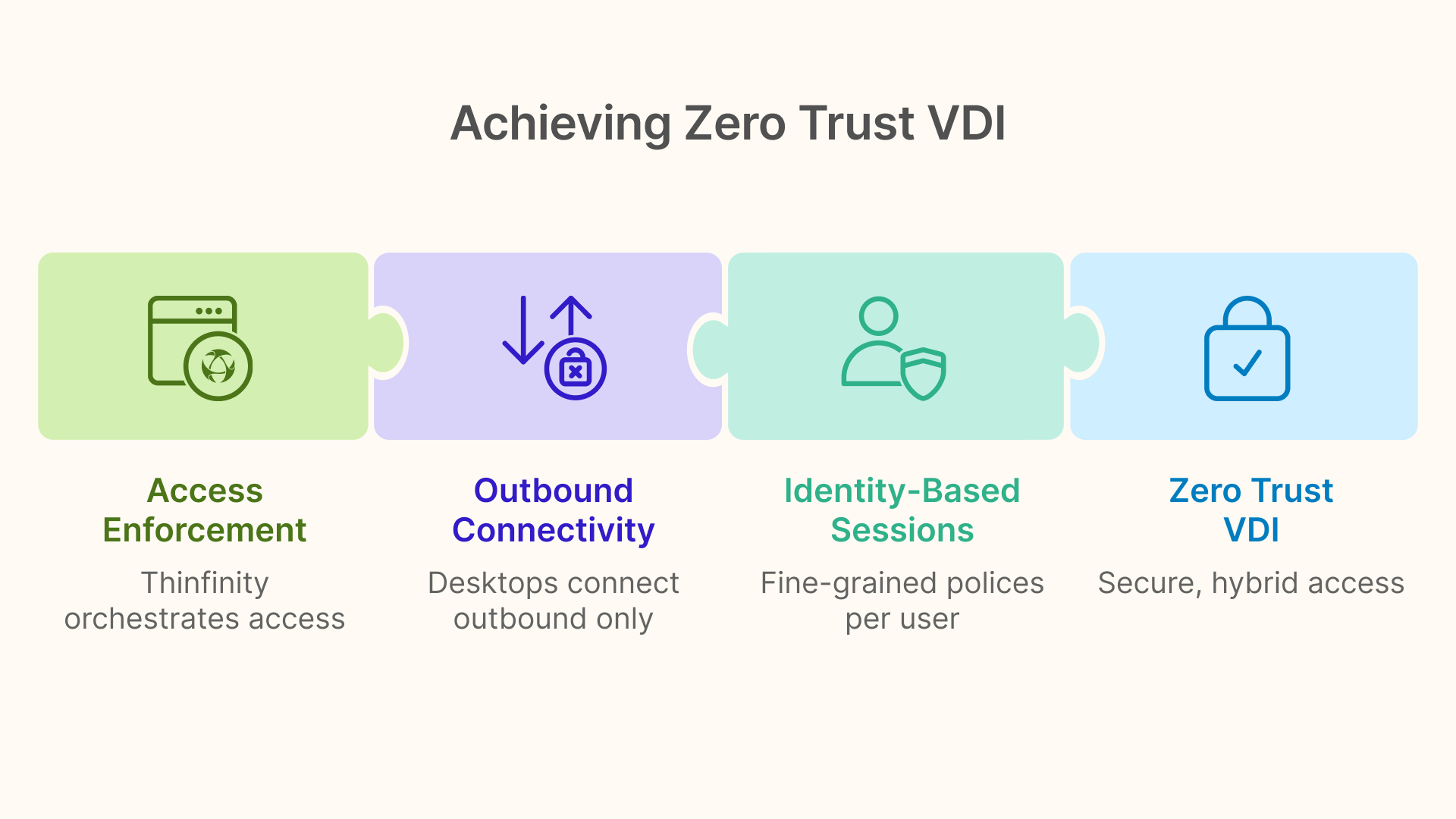
Access Enforcement Without Network Trust
In Zero Trust VDI architectures deployed on cloud platforms such as OCI, Thinfinity Workspace typically operates as an access enforcement and orchestration layer rather than a network extension.
This enables:
- Outbound-only connectivity from desktops and applications
- No exposed inbound services
- Identity-based session creation
- Fine-grained access policies per user and resource
Importantly, this model supports both on-premises and cloud-hosted resources without collapsing them into a single trusted network.
Supporting Hybrid and Transitional Environments
Many universities adopt Zero Trust incrementally. Thinfinity-based architectures support coexistence with legacy access models while progressively reducing VPN dependency. This allows institutions to improve security posture without forcing abrupt operational change.
Governance, Auditing, and Institutional Accountability
Visibility at Academic Scale
Universities require clear answers to fundamental questions:
- Who accessed which resources?
- When were sessions created and terminated?
- How were shared systems used?
Zero Trust VDI architectures provide session-level visibility that traditional network-based models cannot.
Aligning with Regulatory and Internal Requirements
While education is less regulated than healthcare or finance, institutions still face data protection obligations and internal governance standards. Identity-driven access and centralized auditing simplify compliance without adding overhead.
Conclusion: Zero Trust Is the Future of Secure Academic VDI
In education, openness and security must coexist. VPN-based access models, while familiar, increasingly undermine both goals.
Zero Trust VDI offers a more resilient approach—one that aligns with the realities of academic environments, supports diverse users, and reduces systemic risk without sacrificing usability.
As discussed in the pillar article “Traditional VDI vs Cloud VDI for Education: Reliability, Cost, and Scale in 2026,” security and reliability are inseparable. Universities that adopt Zero Trust principles within their VDI architectures position themselves for sustainable, secure digital learning in the years ahead.